Vendor access monitoring in most organizations stops at the VPN log. It tells you one thing: someone connected. What happened next remains unknown.
Vendor remote access is a standard part of how modern IT operates. Vendors need access to your network for service support, system administration, or device reconfiguration. That is normal and in many cases essential.
The challenge appears when something goes wrong. A system stops responding, and there is no data to explain what happened or when. VPN logs record the connection, but not the activity that followed. Without that information, investigating an incident means relying on assumptions rather than facts.
What you need in those moments is network visibility: the ability to see in real time and retrospectively which systems were accessed, over which protocols, how much data was transferred and in which direction.
This article addresses two questions IT teams commonly face when dealing with external access:
✔️How do you monitor and audit the activities of external vendors in your network?
✔️How do you detect unauthorized 4G/5G routers that bypass your security policies?
How to Audit External Vendor Activity in Your Network?
VPN provides access to a network segment, not to a specific service or application. In practice, this means that once a supplier connects, they can potentially reach far more systems than their work actually requires. Some organizations consciously reduce this risk by restricting access to specific hosts and ports, or by using dedicated jump servers. In practice though, this is not common.
A more modern approach is ZTNA (Zero Trust Network Access), which operates on a different principle. Instead of opening up a network segment, it grants access exclusively to the specific service or application the user is authorized for. Nothing beyond that is reachable. For most organizations, however, the switch to ZTNA is not yet on the agenda. Their VPN solution works, it often comes included with their firewall, and that is good enough for now.
Beyond the connection log
VPN logs record who connected and when. Network flow monitoring goes further. It captures:
- which systems were accessed,
- over which protocols,
- how much data was transferred,
- in which direction,
- which files were copied,
- which commands were executed.
How it works in practice
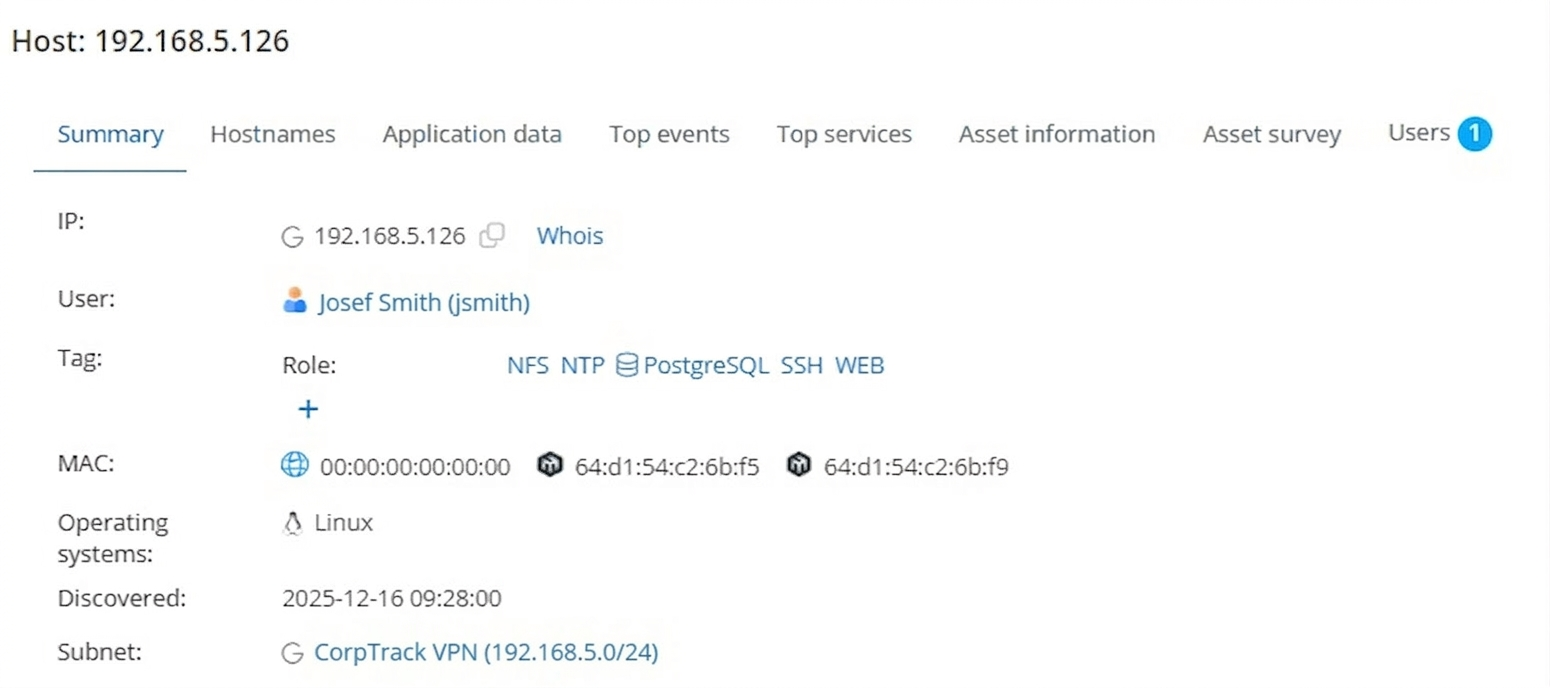
To bridge this gap, organizations are turning to Network Detection and Response (NDR) solutions like Mendel. It monitors network traffic passively and without agents. Once a vendor connects via VPN, it captures all communication generated by their device and links it to a specific user. Where vendor accounts exist in Active Directory or LDAP, that attribution happens automatically. The result is a complete activity record for the entire duration of the connection, available both in real time and retrospectively. Historical data is retained for months to years depending on storage capacity.
When a Vendor Brings Their Own Access to Your Network
Alongside VPN, there is another form of remote access that IT teams often do not know about. A service organization or vendor installs a 4G/5G router in your network to maintain permanent and convenient access for resolving outages, reconfiguring devices or providing remote support. The intention is usually good. The result is always the same: an access point appears in your network that bypasses your security policies and that nobody approved.
Managing third party access to your network assumes that you know how that access works. An unauthorized router breaks that assumption entirely. The vendor connects outside of VPN, outside of any monitoring, and outside of any audit trail.
Why OT Networks Are Especially Exposed
OT networks run on stability. Devices have fixed roles, communication follows consistent patterns, and the traffic looks almost identical day after day. That predictability is what keeps production running reliably.
The risk is that most organizations do not have a tool in place to catch that change. The router gets physically connected, starts communicating, and if nobody is actively monitoring network traffic, it can sit there for weeks or months unnoticed. Depending on network architecture and segmentation, that single device can give a third party access ranging from one subnet all the way to the broader internal infrastructure.
How to detect an unauthorized 4G/5G router
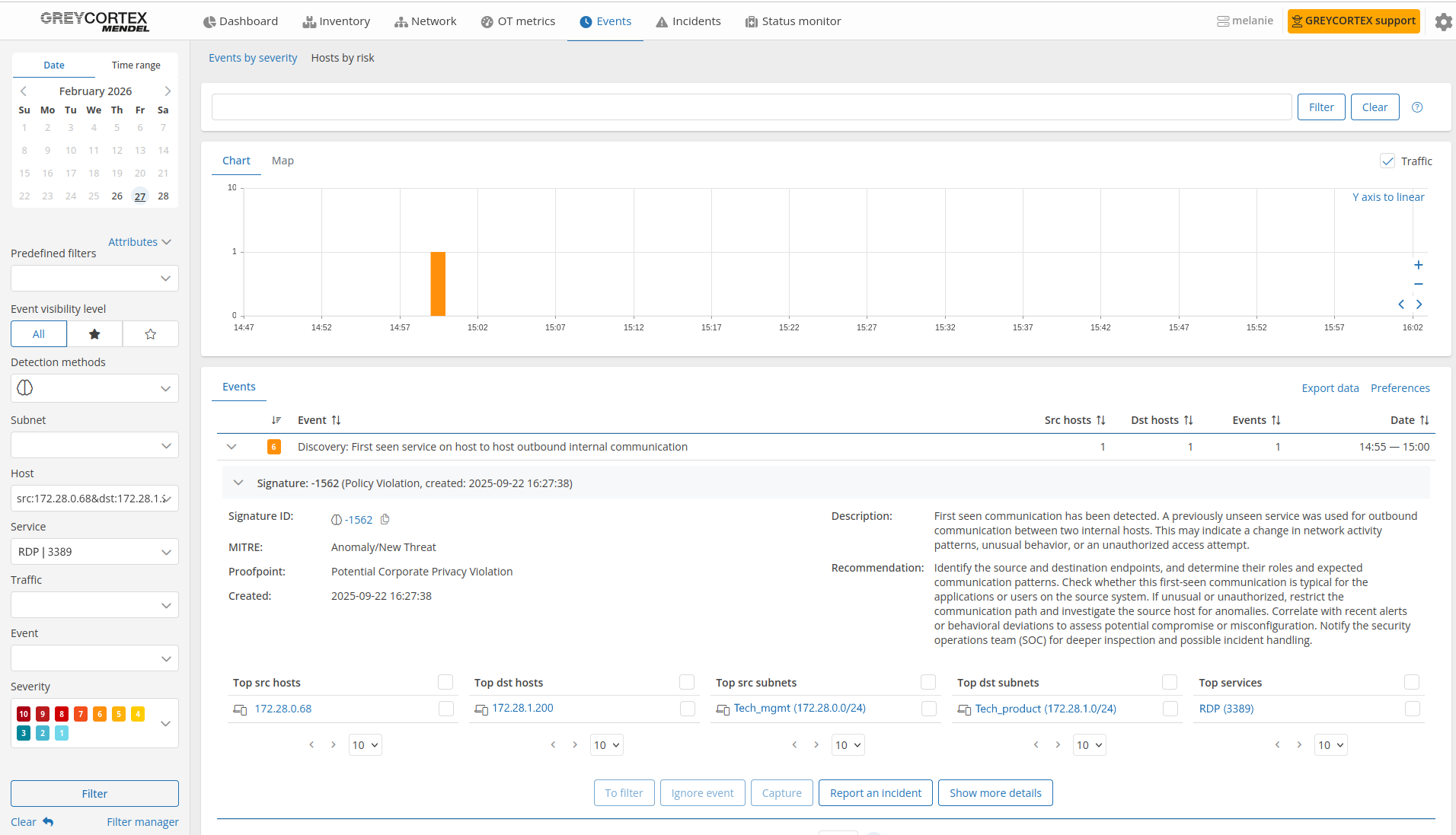
In an OT network, two signals are enough: a new device and a new communication pattern. Mendel detects every new device that appears in a monitored segment, automatically classifies it by role and raises an alert. It also captures situations where a device starts communicating in a way, over a protocol or toward a destination, that has not been seen in that network before. In an environment where traffic is otherwise stable and predictable, these two signals together are a reliable indicator that something has appeared in the network that should not be there.
Building a Verifiable Audit Trail for Third-Party Access
Remote access is not the problem. The problem is not having the data to understand what happened when something goes wrong. Without a clear audit trail of VPN user activity, IT teams are left piecing together incidents from incomplete information.
Mendel gives IT teams something most organizations currently lack: a clear, factual record of what happened in their network and when. That changes how incidents are handled. Instead of spending time gathering statements and making assumptions, teams can go straight to the data. And because that data is retained for months to years, it is available not just for live incidents but for retrospective investigations, audits and compliance requirements as well.
Categories
- Company News (37)
- Product News (27)
- IT/OT Security (40)
- Webinars (6)